The highlight of the week for country managers at SISTRIX is checking updates on the Top 100 list of winners and losers. Website moves, relaunches, company shutdowns, penalties and algorithm changes are easy to spot and always a fun challenge to analyse. Sometimes, however, we spot something a little different. Why did jamesblunt.com get a huge boost…and then a huge loss? It turns out he was hacked.
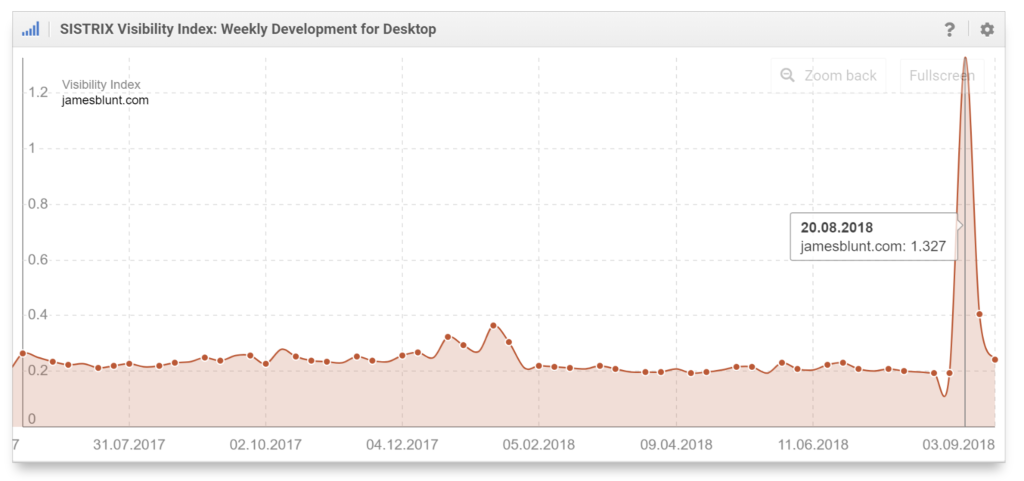
It was late-August when jamesblunt.com appeared to get a huge visibility boost. Winner! The following week James Blunt was in my list of losers.
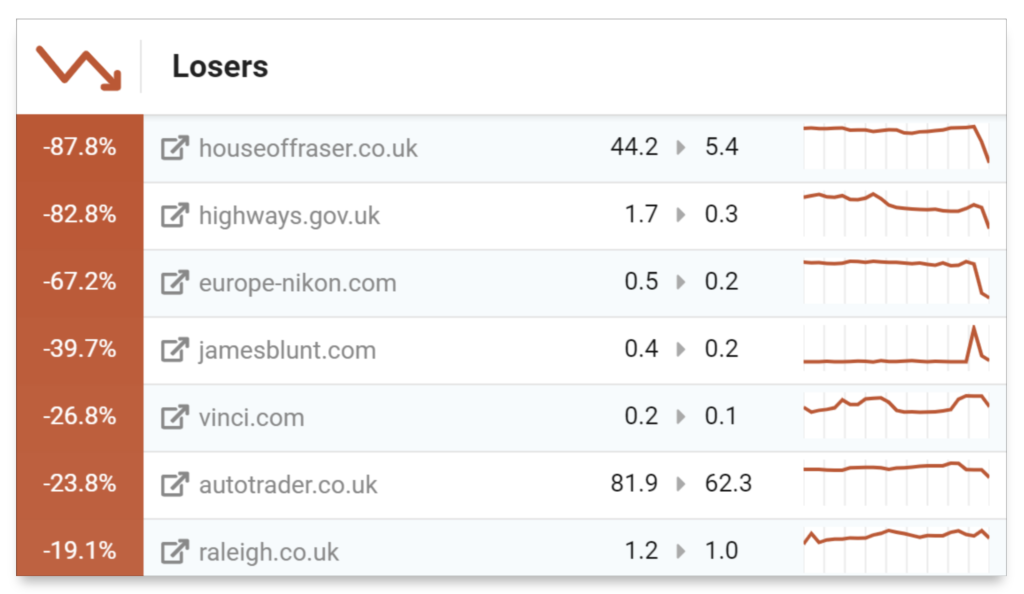
Here’s a list of domain activity from last week in the UK. You’ll see House of Fraser closing down, the UK government highways division deleting the subdomain highways.gov.uk after opening a new site. (No redirects + no content migration = fail!) and europe-nikon.com who are currently going through a migration. But let’s get back to James Blunt. [Update: highways.gov.uk is alive and redirected. They realised that redirects require a live web server! ]
Analysing a visibility peak with SISTRIX.
The process used to analyse a big change in visibility is similar every time.
Start by taking a look at the hosts (subdomains) and directories (paths) to see if the change is spread across the whole domain. Big changes in sub-directory visibility indicate possible changes in content. Big domain-wide changes can indicate server config or Google issues.
- Hosts
- Directories
- Dates
- Keywords
- URLs
Remember that we’re continually storing hosts, directories, keywords and URLs that have ranked in the top 100 Google search results for our core database of one million keywords in the UK. More about our daily visibility update below.
Hosts
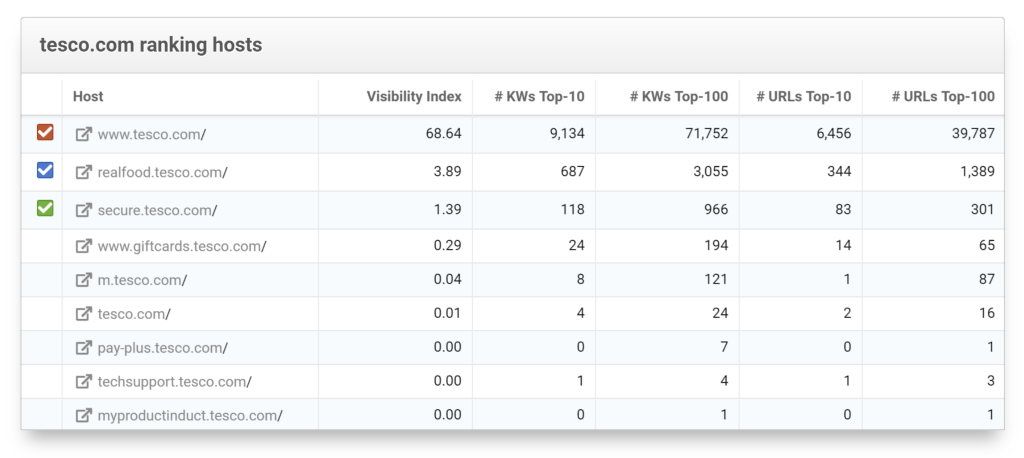
By analysing hosts we’re often able to see features of a website that lie outside the main content management system. At this point, let’s take a moment to inspect a big website.
We’ve seen everything from mobile websites to beta sites listed as hosts (subdomains) and if you’re doing competitor analysis it’s often very revealing. New and failed projects often get exposure here and our historical data set makes information available across all the domains for up to 8 years in the UK. Take tesco.com for example. In the image below we can see when they started their banking operation and the Realfood online recipe site that still ranks well. Diving down into the ‘pay-plus’ host reveals pre-pay credit card keywords and we can also see a mobile website that still ranks because some pages haven’t yet been redirected. If we wind the date back to 2014 we see the failed Tesco Direct operation, a phone-shop, a book blog (a 2011 attempt to copy Amazon?), flower deliveries and more. Data journalists, take note because there’s a huge cache of information here.
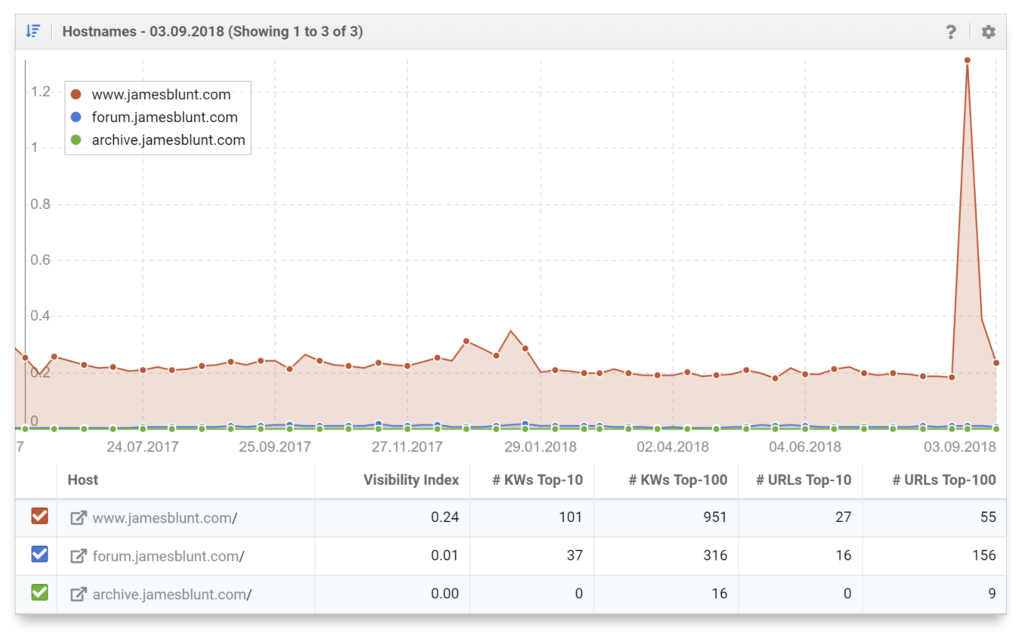
For jamesblunt.com we just see the www host, a forum and an archive that hosts an old forum. Interesting here is the spike only appears on the www host. This indicates that there’s something happening in terms of content on the main website. Did James add a bunch of content?
Directories
The second step is to take a look at directories on that host to see where the change occurred. Subdirectories often lead to dates or new content that has been imported into a sub-directory which provide tips about where the change occurred. Again, we only see activity in the top level directory.
At this point it’s time to start looking into keyword rankings and URLs. To do this, we note the start and peak date of the major change in visibility. The change started after 13.08.2018 and peaked on 20.08.2018.
Ranking changes.
Under Ranking Changes in our Toolbox we can see the complete history of how a site ranked for keywords in our common database. All dates, all keywords and all domains are available to explore.
A quick, large rise in visibility will often occur through gains in a completely new set of keyword rankings. In some cases it’s Google just testing, in other cases it’s because of new content. In this case, taking the dates above and checking for New Keywords we see…
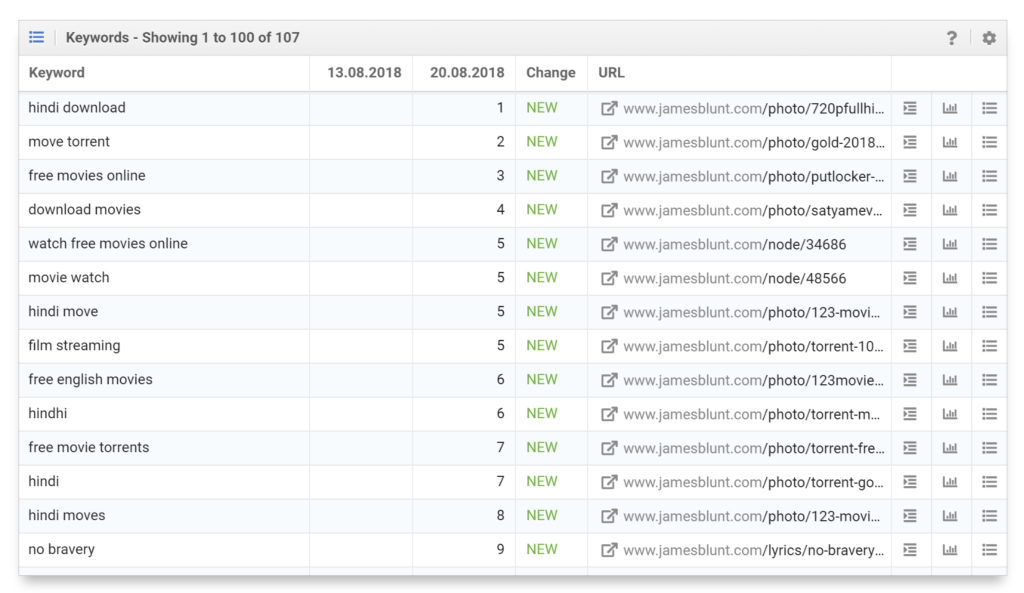
107 new keywords are shown for the week and nearly all are related to movies, torrents, streaming and downloads. Jamesblunt.com was hacked.
Using the weekly index updates the hack was visible on the 20th August.
Since we enhanced our Toolbox with daily visibility updates, however, the change is visible on the 17th August. OK, that’s bad news for the SEO on a Friday but 3 days earlier; An opportunity to rescue 3 days worth of business. James doesn’t have a big transactional element in his website but imagine it was a garden furniture retail website, during the first hot weekend of the year.
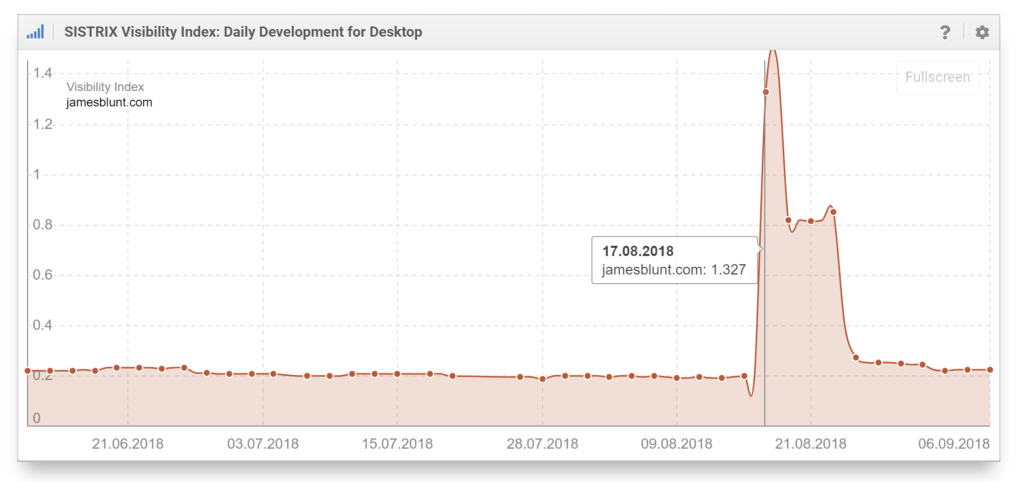
Props to the James Blunt web team. It looks like they managed to clear the problem quickly. Had the SEO, or even the webmaster, been using the daily Visibility Index updates they would have seen that Google had removed the rankings after 7 days. Today, jamesblunt.com is exactly where it was.
Analysing the hack.
What exactly was the content that caught Google’s attention? Our URL database shows the ranking URLS so from there we can start to investigate. Here’s an example.
/photo/720pfullhindi-hd-full-blazing-samurai-download-movie-33551
The URL is still available on the website, but there’s no content on the page. (SEO Tip: Clear out that thin content soon.) The same applies for all the URLs we tested. However, archive.org scanned the site on the 15th of August and captured a page for us.
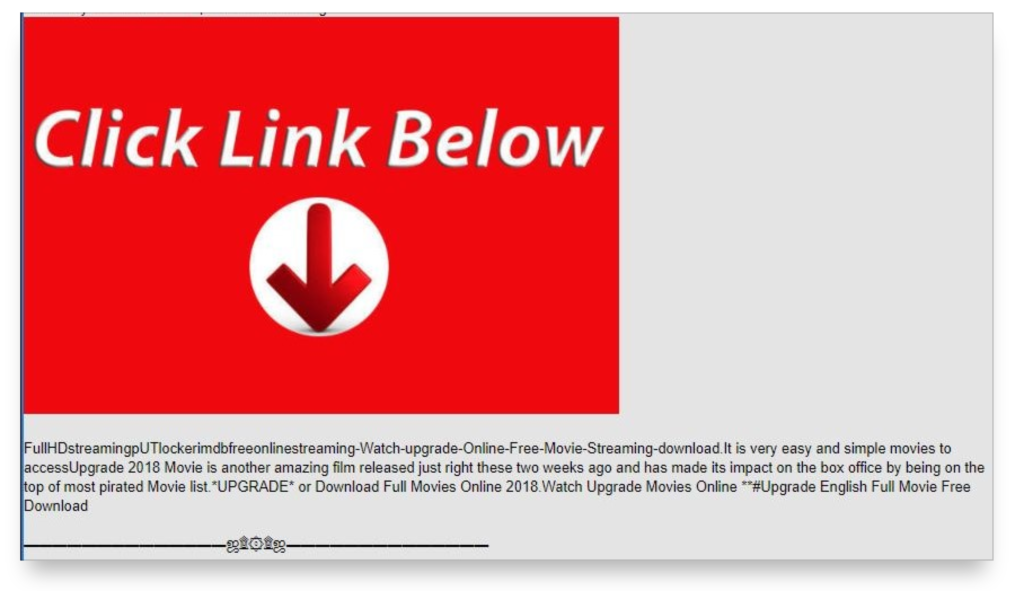
Shortened URLs in the page do indeed lead to a website that streams films.
By searching for parts of the URL and content on that page I was able to find a number of hacked sites.
Two of the websites I found were also for Warner Music musicians and by looking at some of the HTML source it was clear that they are, as is jamesblunt.com, using the same CMS. A little more analysis reveals that there’s a Drupal system behind it and, surprise, they are all using the same template. Is that template still supported? No.
Summary.
Our daily visibility index update is something that SEOs can use for quick feedback on changes happening within Google SERPs. The data allows analysis of SERPs changes which can be useful for highly competitive words. ‘Trump’ for example, is probably being monitored by media outlets right now. URLs are useful for change analysis and, as we see here, analysing a hack.
